BRUCEB NEWS
Bruceb News Is Being Upgraded
Fear not! Bruce is still writing, now at arrgle.com. Read the articles, subscribe to the newsletter, buy the books! There's a story behind the name "Arrgle." In our books, the future belongs to Arrgle. Arrgle is a giant tech company. Thirty years from now, it’s the...
Meta Quest 3: Great VR Device But Where’s The Excitement?
The Quest 3, Meta’s new VR headset, is now on sale. If you’ve ever thought about trying virtual reality, it’s time to jump in. The Quest 3 has excellent specs for the price. It...
Augmented Reality: The State Of The Art In 2023
In the last article we talked about Xreal Air glasses and competitors. They look like sunglasses but when you put them on you can see a giant screen in the air a few feet in...
Augmented Reality Glasses: A Short Step Down A Long Road
You can buy glasses today that show you a huge screen hanging in the air a few feet in front of you. The display is crisp and clear. It looks like you’re watching a movie or...
The Future Of Virtual Reality Is So Bright You Need Shades
VR – virtual reality – is about to get its moment in the sun. That means increased sales for a new generation of devices and games, but more importantly it reflects an uptick in...
RIP Cormac McCarthy
"I had two dreams about him after he died. I dont remember the first one all that well but it was about meetin him in town somewheres and he give me some money and I think I lost...
More Missing Pieces From Apple’s Vision Pro Presentation
In the last article I described a few things missing from Apple’s introduction of its new AR/VR ski goggles spatial computer, Vision Pro. Take the time to watch this six-minute...
What’s Missing From The Apple Vision Pro Headset
On Monday Apple introduced its long awaited new AR/VR headset, the “Apple Vision Pro,” along with a new operating system designed to work in the 3D environment seen through the...
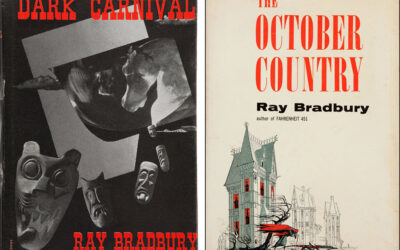
Ray Bradbury And Dark Carnival
The best time to read Ray Bradbury stories is when you are thirteen years old. The second best time is right now. When I was 13, I read The October Country, a collection of some...
Privacy Is Impossible In The Metaverse (And Everywhere Else)
A new study from researchers at UC Berkeley concludes that virtual reality users can be uniquely identified within a few seconds by looking at the way they move their head and...
What’s Next For ChatGPT And The World?
A lot of people write words. Many of them do a modest amount of research and draw on a modest amount of creativity, then they put a modest amount of work into their words. That...
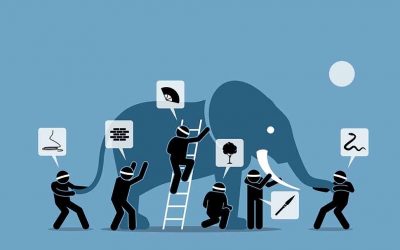
ChatGPT Is The Elephant In The Room
Remember the parable of the blind men and the elephant? Each person draws different conclusions about the elephant based on their limited experiences. ChatGPT is the elephant in...
Why Mark Zuckerberg Dreams About Roblox
Over half of all US kids and teenagers under the age of 16 play Roblox every month. Read that again. Over half of all US kids and teenagers under the age of 16 play Roblox every...
Mark Zuckerberg Is Right About The Metaverse
You're convinced Mark Zuckerberg will fail, right? A little more than a year ago Zuckerberg renamed Facebook to "Meta." He is investing billions of dollars in virtual reality and...
It’s Time To Leave LastPass
LastPass was hacked. It was a bad, bad hack. If you use LastPass, your passwords are probably fine. LastPass uses a very secure method to protect your secrets. You don't have to...
My Top Ten List Is Not The Same As Your Top Ten List
Here’s my 2022 Spotify Top Ten playlist. You’ve never heard any of my top songs. With one or two exceptions, you’ve never heard of any of the artists. That’s okay. I’ve never...